-
How to CISO, Volume 1: The First 91 Days

Just want to download the eBook? Head over to How to CISO, Volume 1: The First 91 Days! It seems to be a rite of passage for all CISOs to, at some point in their career, write down their advice for other CISOs starting a new job, whether they are a first-time or veteran CISO.…
Security Talks
-
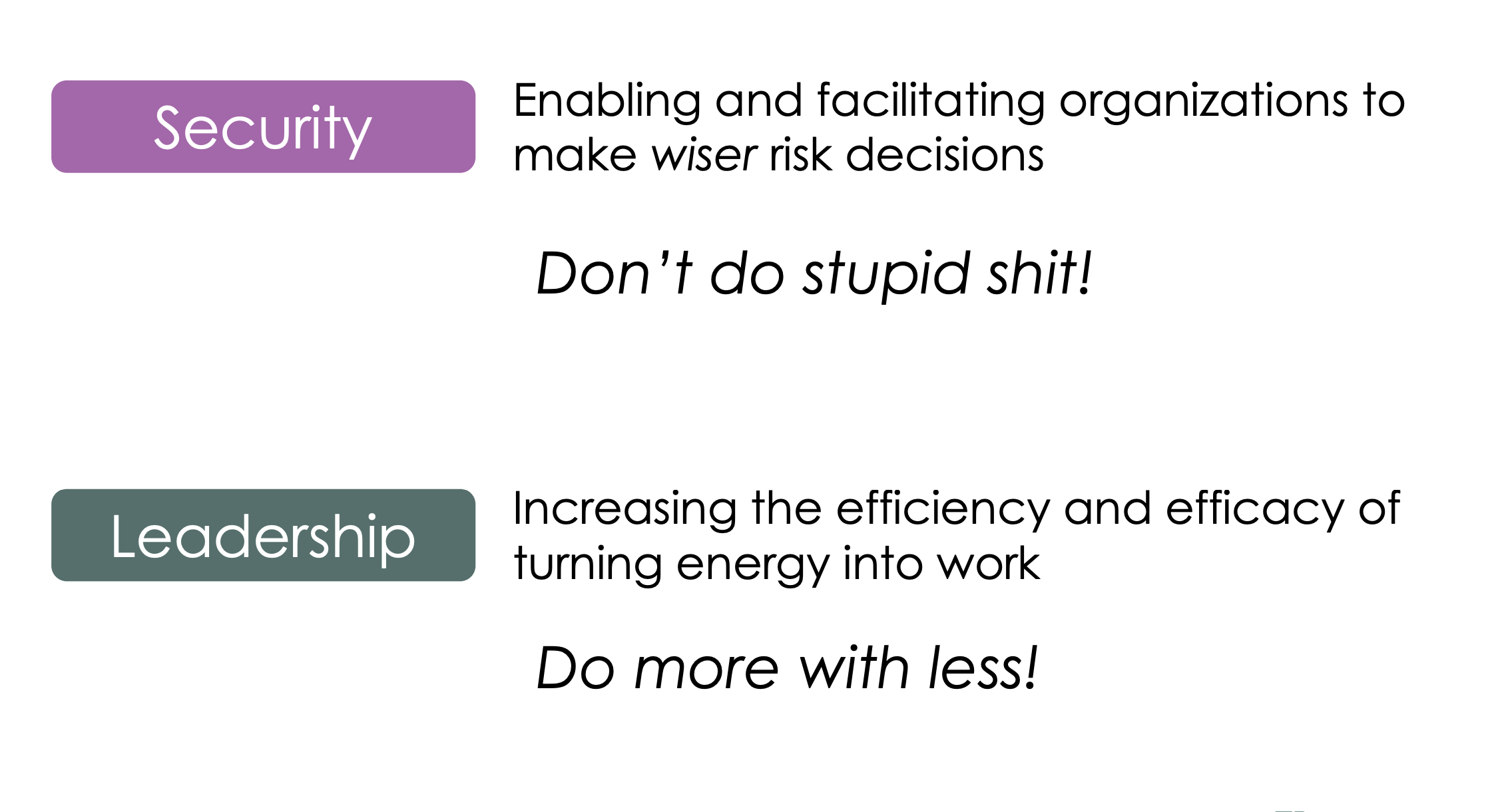
This talk delves into the intersection between security–helping make wiser risk choices–and leadership–getting more done with a lower energy cost. It draws on the lessons of the Six Leadership Disciplines and Humans are Awesome at Risk Management talks, providing a handful of examples of specific leadership skills to practice. The 24 skills in the matrix…
-
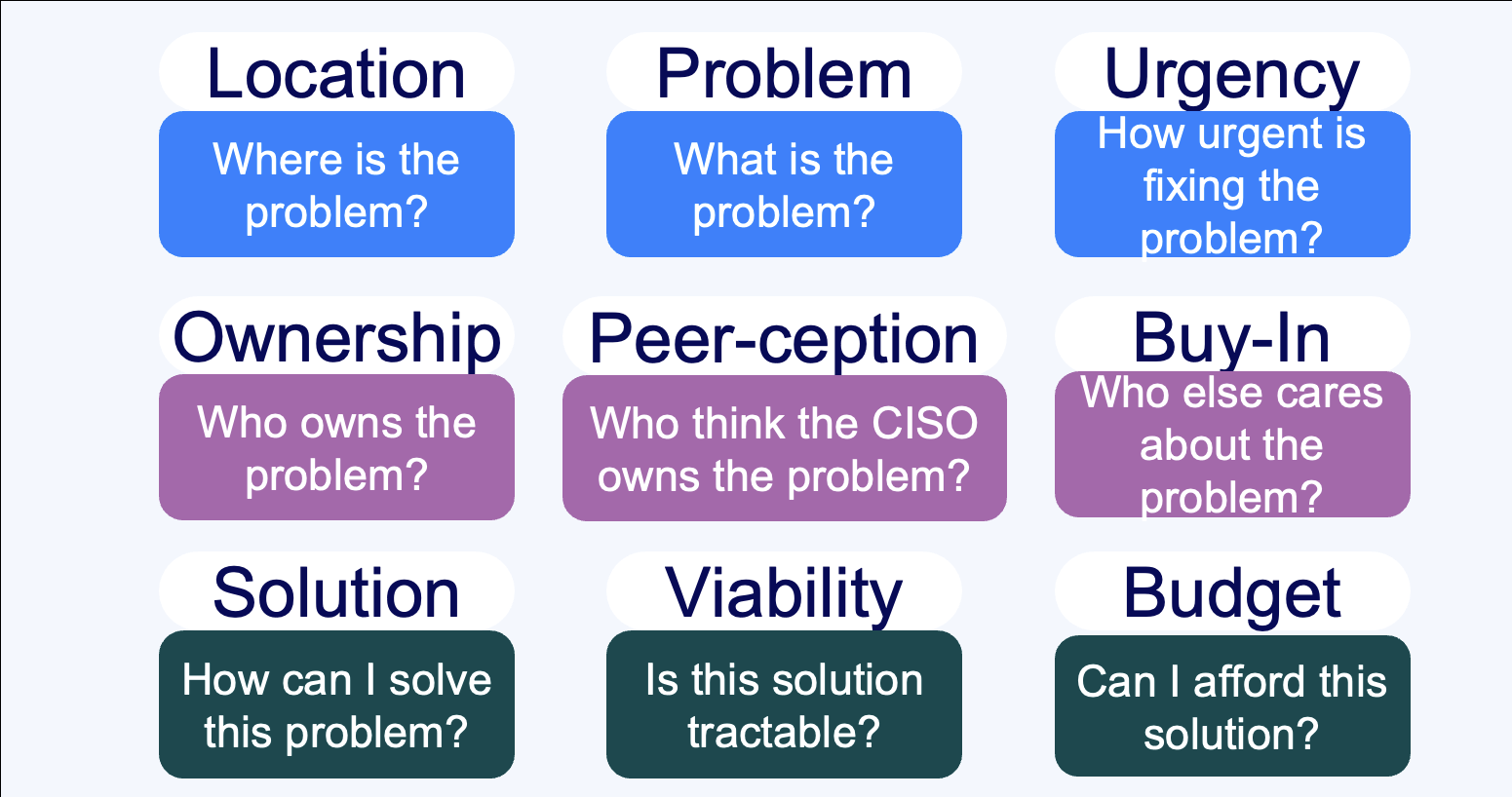
Summary Everybody sells, right? Wrong. Unless you’re taking an order and retiring your quota, you don’t sell – instead, you market. If you’re selling to a CISO, you need to understand the organizational dynamics that surround a CISO’s decision-making process. This talk walks through nine critical questions that CISOs need to understand the answers to…
-
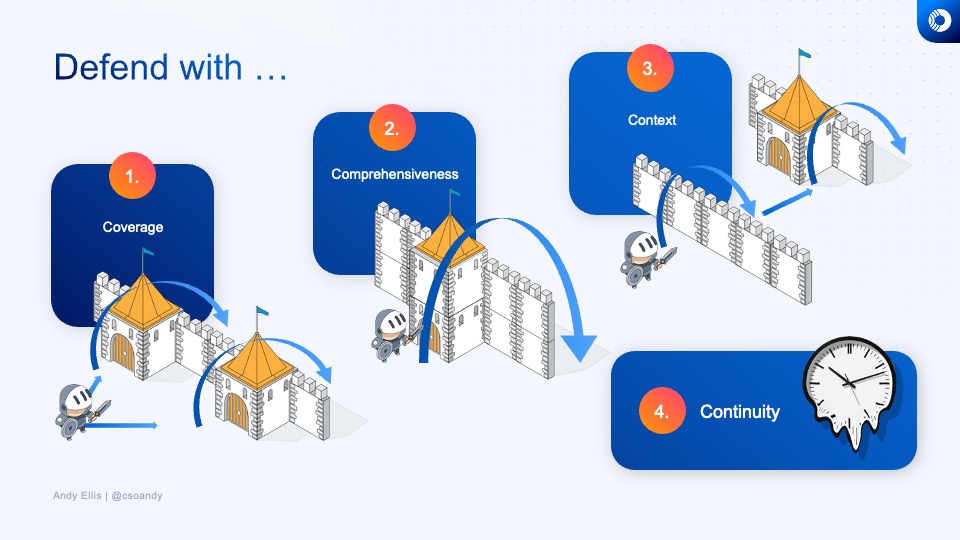
How do you know what to invest in next, or whether the time and energy that you’re spending on a security technology or program is a good investment? Learn how veteran CSOs think about security investments, and develop your own rubric for evaluating where to best make your next security improvement.
-
How do you design defenses against DDoS? And how do you think about them from a policy perspective?
-
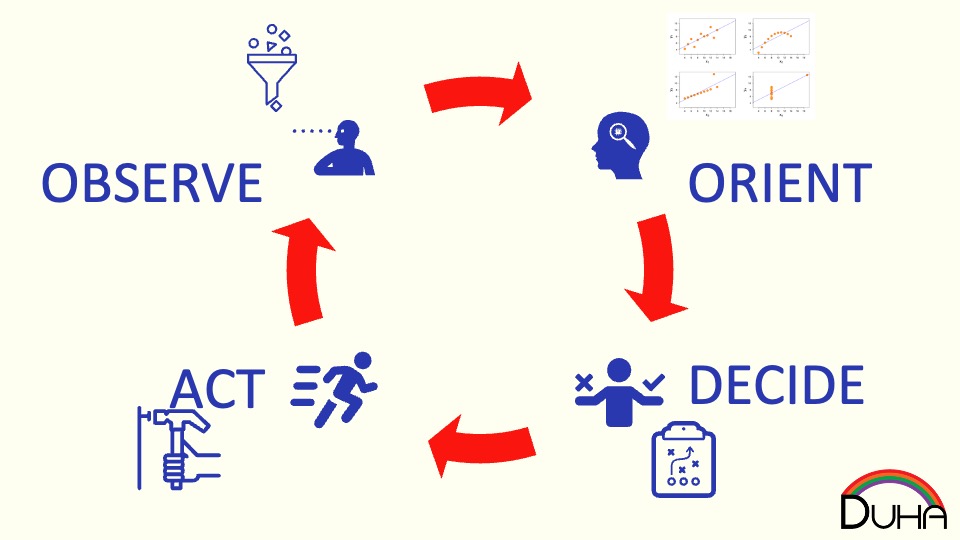
How do humans make risk decisions, and are they good, bad, or something else?
-
How do the grand challenges of the future look like the grand challenges of the past?
-
What does a Zero Trust journey look like? Explore how we migrated Akamai to a zero trust network access model, before that was even a phrase people knew.
Security Panels
-
Investing in Solutions for Tomorrow’s Attacks
Potential investors in the cybersecurity sector need a deep understanding of what the pinch points are for cybersecurity practitioners. Andy Ellis, a 20-year CSO at Akamai who is now an operating partner at YL Ventures, discusses what cybersecurity sectors are attracting investment – and why.
-
Scaling Security Programs in High Growth Companies
This webinar discusses the challenges of scaling security programs in high-growth companies, featuring insights from security experts from HashiCorp and Robinhood.
Security Blog
Security Podcasts
-
CISO Series: How Cisos Make it Worse for other CISOs
https://cisoseries.com/how-cisos-make-it-worse-for-other-cisos/ This week’s episode is hosted by me, David Spark (@dspark), producer of CISO Series and Mike Johnson. Our guest is Andy Ellis (@csoandy), operating partner, YL Ventures. Full transcript (from cisoseries.com) Voiceover Ten second security tip. Go. Andy Ellis You should use multiple Chrome profiles so that you can separate your cookies and log-in credentials between your work and personal…
-
How Many Forms of ID Do I Need to Buy This Gift Card?
https://cisoseries.com/how-many-forms-of-id-do-i-need-to-buy-this-gift-card/ Getting someone to purchase gift cards is a popular vector for theft. Given that the gift card theft technique is so well known, many online sites have put up additional barriers to purchasing gift cards. Trying to buy them legitimately has become increasingly difficult. This week’s episode is hosted by David Spark (@dspark), producer…