-
How to CISO, Volume 1: The First 91 Days

Just want to download the eBook? Head over to How to CISO, Volume 1: The First 91 Days! It seems to be a rite of passage for all CISOs to, at some point in their career, write down their advice for other CISOs starting a new job, whether they are a first-time or veteran CISO.…
Security Talks
-
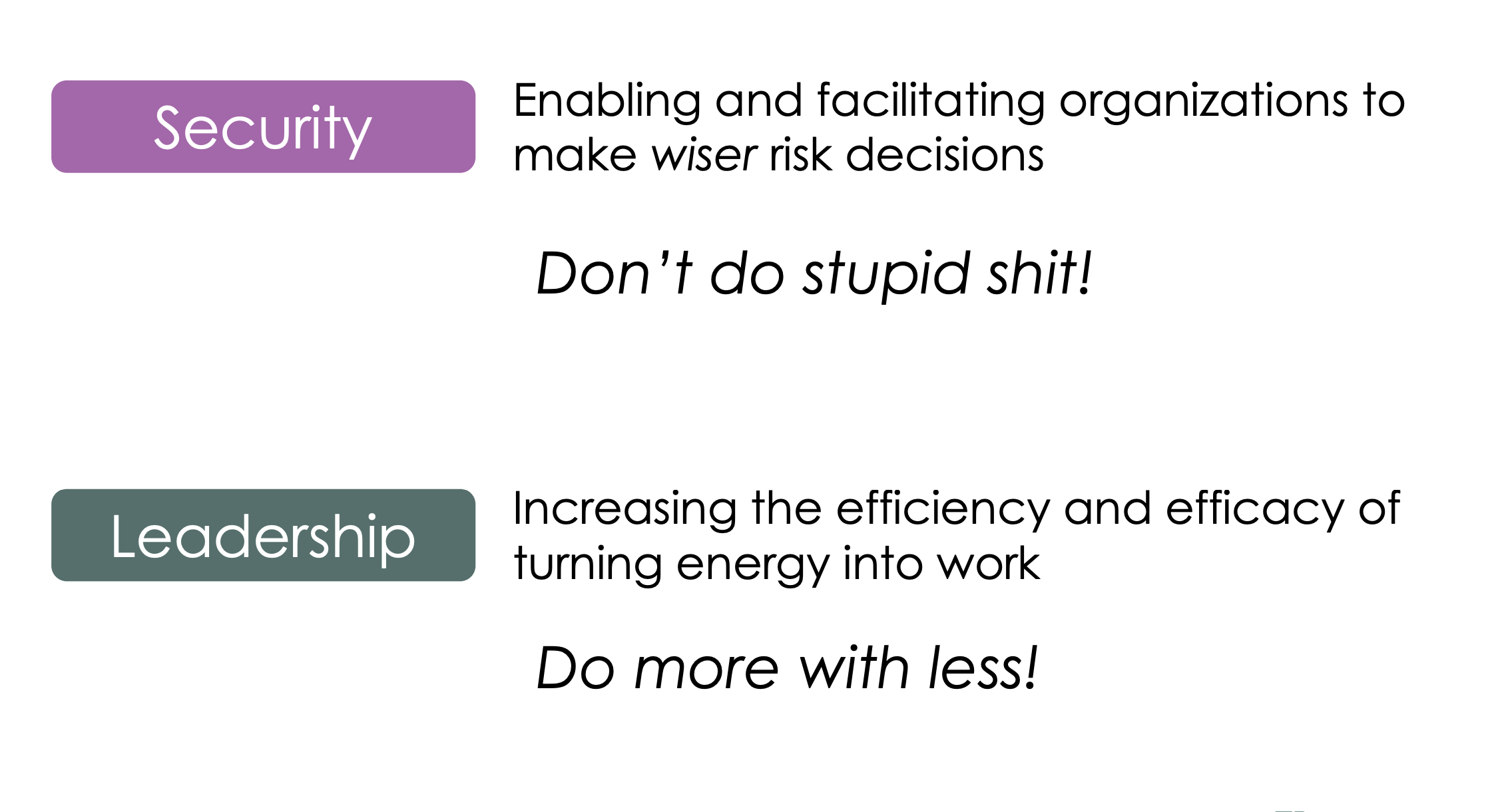
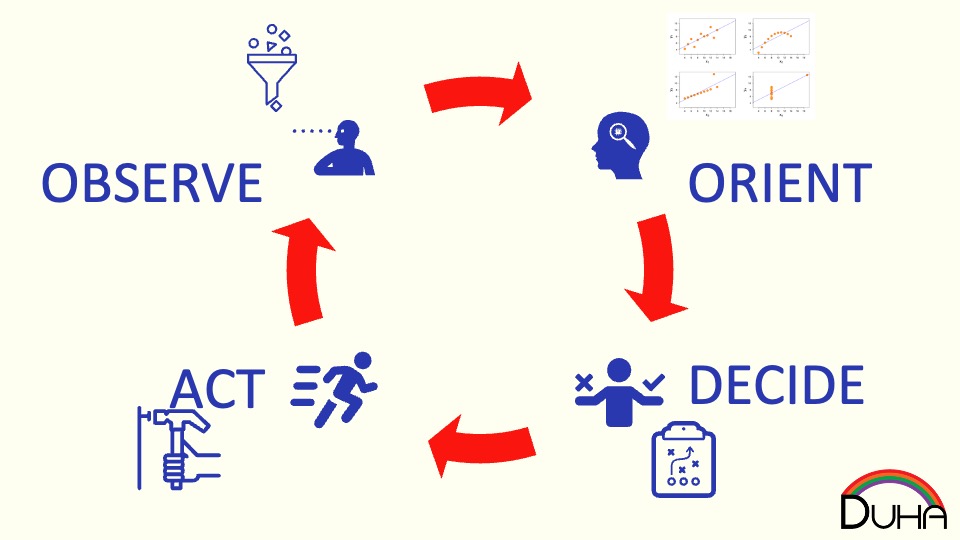
This talk delves into the intersection between security–helping make wiser risk choices–and leadership–getting more done with a lower energy cost. It draws on the lessons of the Six Leadership Disciplines and Humans are Awesome at Risk Management talks, providing a handful of examples of specific leadership skills to practice. The 24 skills in the matrix…
-
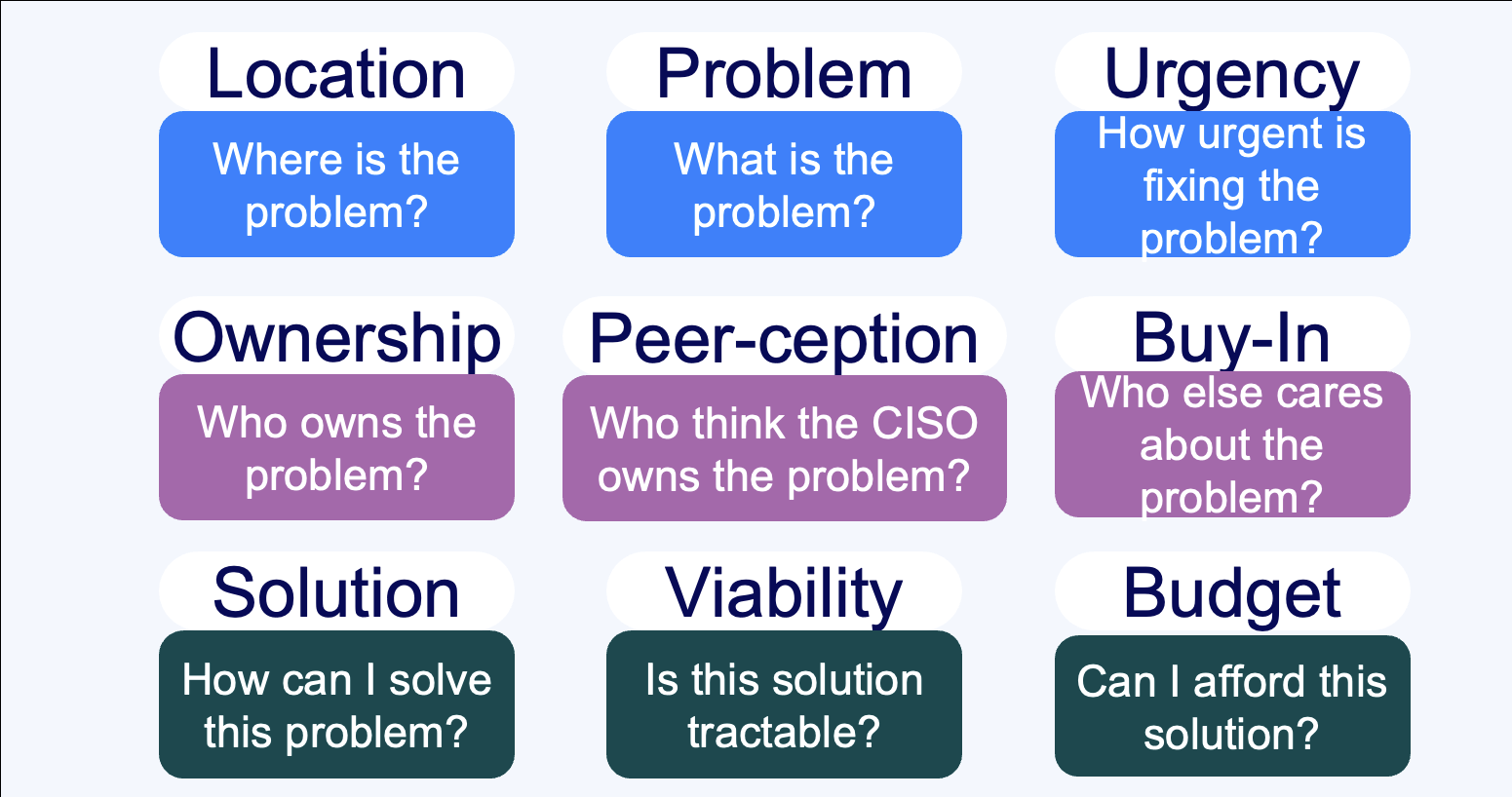
Summary Everybody sells, right? Wrong. Unless you’re taking an order and retiring your quota, you don’t sell – instead, you market. If you’re selling to a CISO, you need to understand the organizational dynamics that surround a CISO’s decision-making process. This talk walks through nine critical questions that CISOs need to understand the answers to…
-
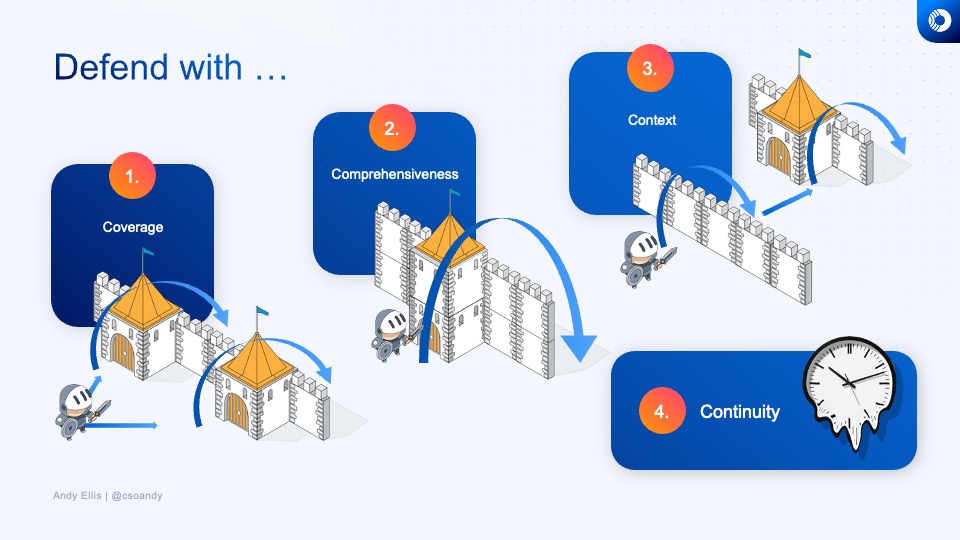
How do you know what to invest in next, or whether the time and energy that you’re spending on a security technology or program is a good investment? Learn how veteran CSOs think about security investments, and develop your own rubric for evaluating where to best make your next security improvement.
-
How do you design defenses against DDoS? And how do you think about them from a policy perspective?
-
How do humans make risk decisions, and are they good, bad, or something else?
-
How do the grand challenges of the future look like the grand challenges of the past?
-
What does a Zero Trust journey look like? Explore how we migrated Akamai to a zero trust network access model, before that was even a phrase people knew.
Security Panels
-
Lenovo Late Night I.T: Cybersecurity: Trust No One
Join Baratunde Thurston, Tim Brown, and Andy Ellis as they demistify security.
-
Cyberweek 2021: Navigating the CISO-Vendor relationship
The panel discusses the do’s and don’ts of engagements between CSOs and early-stage startups, the concerns around long integration cycles, the value in quick implementations, and the need to show value quickly.
-
Cyberweek 2021: YL Ventures & Scale Fireside Chat
YL Ventures and Scale Venture Partners hosted a Cyber Week 2021 Fireside chat where Wendy Nather, Sounil Yu, Ryan Gurney, and Ariel Tseitlin discussed the cyber industry challenges and trends. They talked about the burning challenges and the basics that CSOs are still struggling with, and how ransomware attacks undermine our ability to recover. Other…
Security Blog
-
Password weakness
In the xkcd comic on password strength, Randall Munroe triggers a discussion on the effectiveness of password algorithms. While he raises valid points, the real risk lies in password reuse and breaches. Moving away from passwords and exploring alternatives like SSL certificates or one-time passwords may be a more promising approach.
-
How certificates go bad
The recent Comodo sub-CA bogus certificate issuance has sparked a loud discussion in the security community. This incident highlights the flaws in the SSL certificate authority (CA) model. Trusting numerous CAs globally creates vulnerability, and compromised registration authorities (RAs) can issue certificates for any domain. Incident response and transparency are crucial, but incidents like this…
-
Architecting for DDoS -Defense
Designing a robust DDoS mitigation strategy requires understanding potential failures and the efficiency of attacks. While increasing capacity can be a simple solution, it’s crucial to push functionality to the edge, prioritize user authentication, employ caching techniques, and store user-generated content. Instead of focusing on recovery time, design for a Minimum Uninterrupted Service Target to…
-
Awareness Training
Implementing a robust security awareness program is not difficult if your company prioritizes security. However, if security is not a concern, you have a significant problem. Many programs focus on meeting auditor requirements with annual training sessions and policy acknowledgments. While these are necessary, a comprehensive program integrates security into various activities and encourages employees…
-
NSEC3: Is the glass half full or half empty?
NSEC3 is a DNSSEC specification that addresses the issue of authenticated denial of existence in DNS. It replaces the NSEC method by using a hashing function and signed hash ranges to prevent easy collection of zone file contents. While NSEC3 improves secrecy, it raises questions about the need for semi-secret public DNS names and suggests…
-
Contracting the Common Cloud
After attending CSO Perspectives, Bill Brenner has some observations on contract negotiations with SaaS vendors. While his panel demonstrated a breadth of customer experience, it was, unfortunately, lacking in a critical perspective: that of a cloud provider. Much of the point of SaaS, or any cloud service, in the economy of scale you get; not just in…
-
The Adaptive Persistent Threat
Much ado has been made of the “Advanced Persistent Threat”. Unfortunately, pundits look at the ease of some of the attacks, and get hung up on the keyword, “Advanced.” How do we know the adversary is so advanced, if he can succeed using such trivial attacks? The relative skill of the adversary is actually uninteresting;…
-
Why is PCI so successful?
At the RSA Conference, participating in a panel discussion on the PCI Data Security Standard, it was evident that PCI has significantly impacted the industry. The standard’s simplicity, broad applicability, and narrow focus on protecting specific data have improved security more than any other standard. It serves as a model for future compliance standards.
-
Why don’t websites default to SSL/TLS?
HTTP is designed for web administrators to host multiple sites on fewer systems, while HTTPS (SSL/TLS) focuses on security-conscious users. SSL’s design creates scalability issues, although solutions like wildcard and SAN certificates, as well as SNI, aim to mitigate them, pending widespread SNI support.
-
Modeling Imperfect Adversaries
Brian Sniffen’s paper at FAST highlights the importance of understanding adversaries in risk assessment, particularly in the streaming media space. It explores concepts like defense in breadth and tag-limited adversaries, emphasizing the need to consider different capabilities and attack strategies when formulating security frameworks. His work provides valuable insights into the evolving landscape of streaming…
Security Podcasts
-
Entry Level Position Available. 15+ Years Experience Required.
https://cisoseries.com/entry-level-position-available-15-years-experience-required/ That headline is not a joke. An actual job listing on LinkedIn requested just that. We’re all hoping this was an error. Regardless, the community response to it was truly overwhelming, speaking much to the frustration of green and junior cybersecurity job seekers who are truly looking for entry level jobs.This week’s episode is hosted by David…
-
Get All the Stress You Want, With None of the Authority
https://cisoseries.com/get-all-the-stress-you-want-with-none-of-the-authority/ CISOs and other security leaders have a lot of stress. But so do other C-level employees. Why does a CISO’s stress seem that much more powerful? Is it that their job is still in constant development, or is the “C” in their name just in title, but not authority?This week’s episode is hosted by David…
-
Cloud Security Reinvented: Kathy Wang
https://open.spotify.com/episode/3NhKH69mHwhXI70KgNSc15 💡 Guest: Kathy Wang, Chief Security Officer at Discord💡 Noteworthy: Kathy is a security executive and leader with a strong background in project management, research, and business development. She has worked in government, commercial, and technology startup environments and currently advises startups that offer security services/products. Key Insights ⚡ The importance of access control in security. Improving…