-
How to CISO, Volume 1: The First 91 Days

Just want to download the eBook? Head over to How to CISO, Volume 1: The First 91 Days! It seems to be a rite of passage for all CISOs to, at some point in their career, write down their advice for other CISOs starting a new job, whether they are a first-time or veteran CISO.…
Security Talks
-
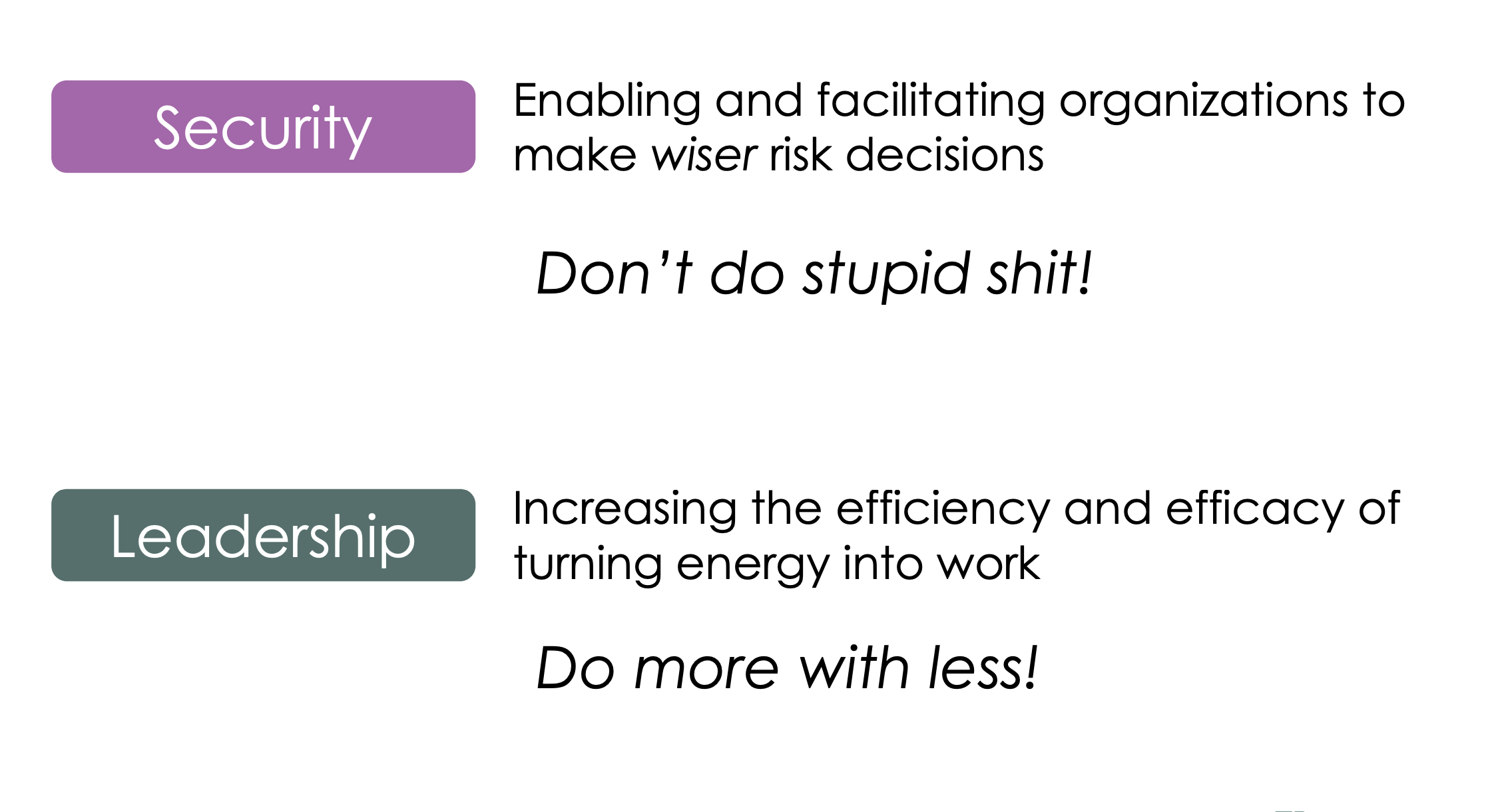
This talk delves into the intersection between security–helping make wiser risk choices–and leadership–getting more done with a lower energy cost. It draws on the lessons of the Six Leadership Disciplines and Humans are Awesome at Risk Management talks, providing a handful of examples of specific leadership skills to practice. The 24 skills in the matrix…
-
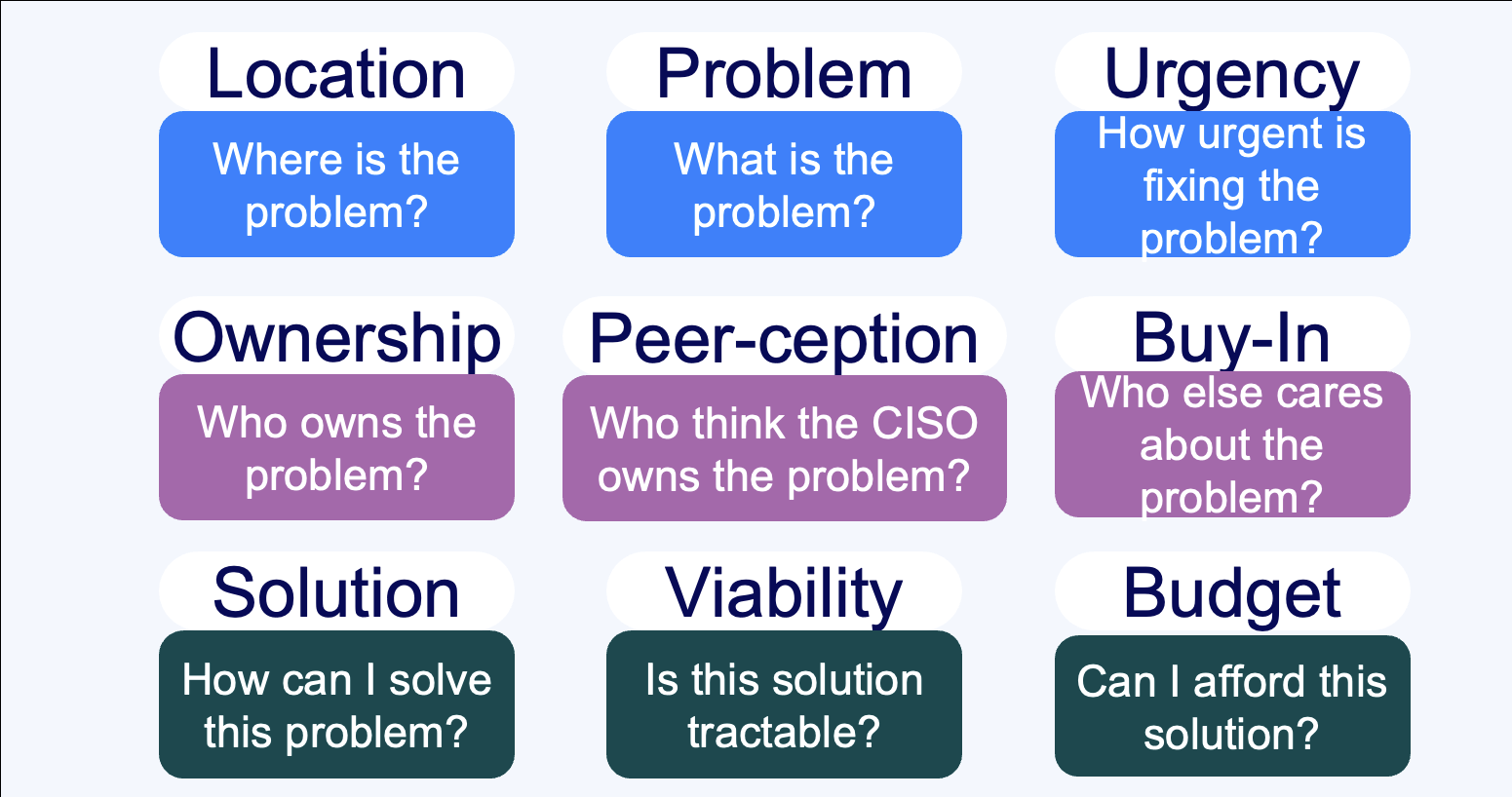
Summary Everybody sells, right? Wrong. Unless you’re taking an order and retiring your quota, you don’t sell – instead, you market. If you’re selling to a CISO, you need to understand the organizational dynamics that surround a CISO’s decision-making process. This talk walks through nine critical questions that CISOs need to understand the answers to…
-
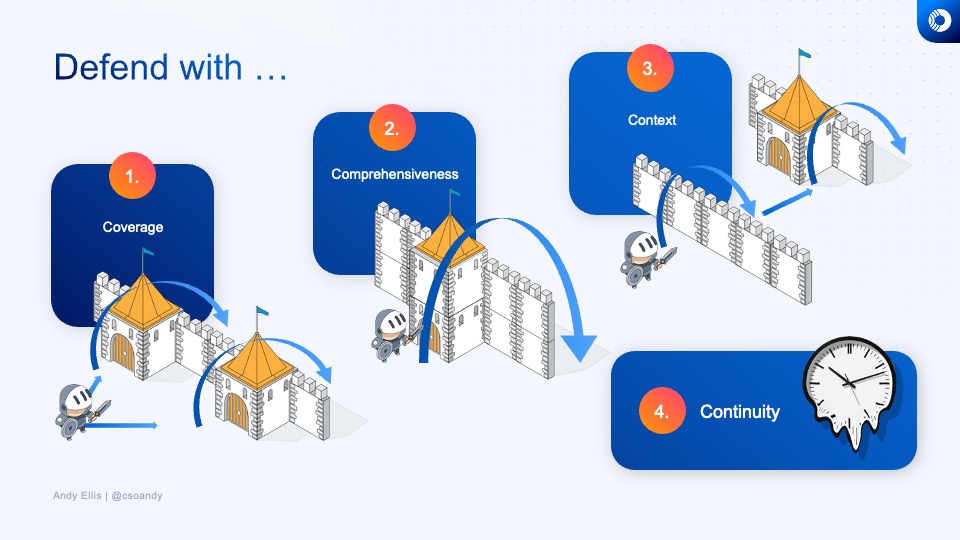
How do you know what to invest in next, or whether the time and energy that you’re spending on a security technology or program is a good investment? Learn how veteran CSOs think about security investments, and develop your own rubric for evaluating where to best make your next security improvement.
-
How do you design defenses against DDoS? And how do you think about them from a policy perspective?
-
How do humans make risk decisions, and are they good, bad, or something else?
-
How do the grand challenges of the future look like the grand challenges of the past?
-
What does a Zero Trust journey look like? Explore how we migrated Akamai to a zero trust network access model, before that was even a phrase people knew.
Security Panels
-
Lenovo Late Night I.T: Cybersecurity: Trust No One
Join Baratunde Thurston, Tim Brown, and Andy Ellis as they demistify security.
-
Cyberweek 2021: Navigating the CISO-Vendor relationship
The panel discusses the do’s and don’ts of engagements between CSOs and early-stage startups, the concerns around long integration cycles, the value in quick implementations, and the need to show value quickly.
-
Cyberweek 2021: YL Ventures & Scale Fireside Chat
YL Ventures and Scale Venture Partners hosted a Cyber Week 2021 Fireside chat where Wendy Nather, Sounil Yu, Ryan Gurney, and Ariel Tseitlin discussed the cyber industry challenges and trends. They talked about the burning challenges and the basics that CSOs are still struggling with, and how ransomware attacks undermine our ability to recover. Other…
Security Blog
-
Infosec – Failing or Succeeding?
Noam Eppel from Vivica contends that Information Security is a complete failure, citing alarming statistics on security breaches and cybercrime. While his article highlights the risks, many dissent from his conclusion, considering it a collection of gloomy statistics often seen in security vendor pitches.
-
False Positives
During my morning commute, I encountered an interesting flaw in an alerting system. My car’s weight sensor triggers an alarm if it detects a possible passenger without a seatbelt. However, this car’s system escalates from a dinging sound to a rapid alarm. My immediate thought was to disable the alarm, highlighting a common security system…
-
Sledgehammers
Achieving perfect data security involves elaborate measures such as encryption, one-time passwords, asymmetric identifiers, and physical access controls. However, the ultimate level of security must align with the data’s value and potential threats, avoiding the extreme sledgehammer argument while striking a balance in risk management.
-
Usenix Security Symposium
The upcoming USENIX security symposium in Vancouver during the first week of August promises an impressive lineup of invited talks. While I may not attend, I highly recommend catching Matt Blaze’s presentation on wiretapping, previously acclaimed as one of the most exceptional research talks at ICNS 2006.
-
Pseudonymity
Pseudonymity refers to adopting a semi-permanent, yet incomplete or false identity, commonly observed in online communities. It allows individuals to use distinctive pseudonyms to establish their unique presence while avoiding full anonymity. This practice fosters better community engagement by promoting courteous interactions. However, the challenge lies in identifying instances where a single person assumes multiple…
-
Disclosure Laws
During a recent conference, a panelist expressed their belief that the California Disclosure Law (SB-1386) was an exceedingly inadequate information security regulation. However, I hold a different perspective. In my view, SB-1386 stands as the epitome of information security regulations, surpassing even the esteemed GLBA. While most regulations focus on prescribing specific controls for safeguarding…
Security Podcasts
-
Who Do You Need to Trust When You Build a Zero Trust Architecture?
https://cisoseries.com/who-do-you-need-to-trust-when-you-build-a-zero-trust-architecture/ Uggh, just saying “zero trust” sends shivers down security professionals’ spines. The term is fraught with so many misnomers. The most important is who are you going to trust to actually help you build that darn zero trust program? Are you going to look at a vendor that’s consolidated solutions and has built programs like this…
-
The Best Interview Questions and the Answers You Want to Run From
https://cisoseries.com/the-best-interview-questions-and-the-answers-you-want-to-run-from/ You want an awesome job in cybersecurity, and you want to ask the right questions. What are the right answers, and which ones are red flags that should cause you to run?This week’s episode is hosted by David Spark (@dspark), producer of CISO Series and Andy Ellis (@csoandy), operating partner, YL Ventures. Our guest is Renee Guttman, former CISO,…
-
It’s OK to Look Like a Cyber Hero. Just Don’t Act Like One.
https://cisoseries.com/its-ok-to-look-like-a-cyber-hero-just-dont-act-like-one/ Security professionals should turn in the cyber hero mentality for the “sidekick” role. Many cybersecurity leaders believe they need to save the company from all the stupid users who can’t protect themselves. The reality is security professionals should lose the saviour mentality for a supporting role where they’re running alongside different business units trying…